Forbes: Cellebrite can unlock every iPhone
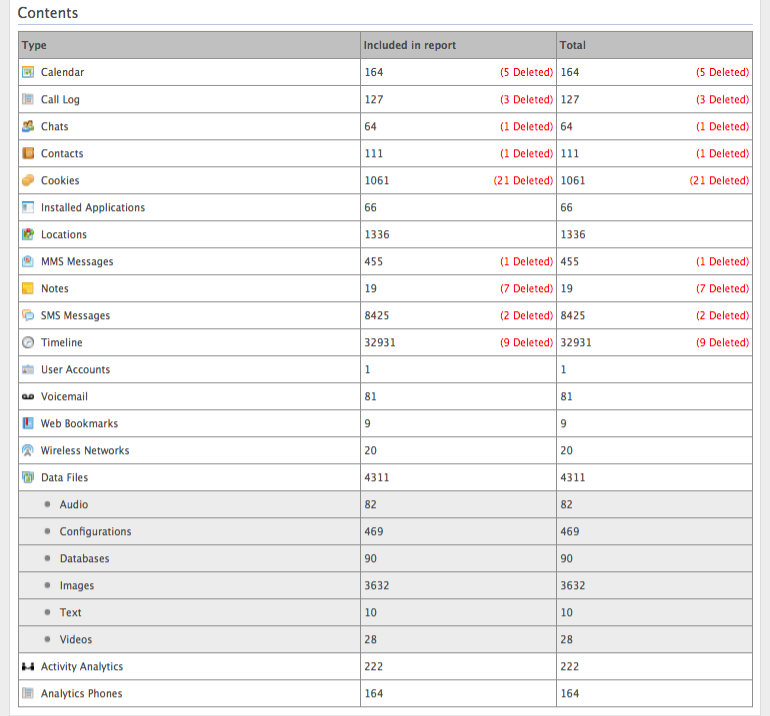
Cellebrite, a Petah Tikva, Israel-based vendor that’s become the U.S. government’s company of choice when it comes to unlocking mobile devices, is this month telling customers its engineers currently have the ability to get around the security of devices running iOS 11 . That includes the iPhone X, a model that Forbes has learned was successfully raided for data by the Department for Homeland Security back in November 2017, most likely with Cellebrite technology.
The Israeli firm, a subsidiary of Japan’s Sun Corporation, hasn’t made any major public announcement about its new iOS capabilities. But Forbes was told by sources (who asked to remain anonymous as they weren’t authorized to talk on the matter) that in the last few months the company has developed undisclosed techniques to get into iOS 11 and is advertising them to law enforcement and private forensics folk across the globe. Indeed, the company’s literature for its Advanced Unlocking and Extraction Services offering now notes the company can break the security of “Apple iOS devices and operating systems, including iPhone, iPad, iPad mini, iPad Pro and iPod touch, running iOS 5 to iOS 11.” Separately, a source in the police forensics community told Forbes he’d been told by Cellebrite it could unlock the iPhone 8. He believed the same was most probably true for the iPhone X, as security across both of Apple’s newest devices worked in much the same way.


 “Data-driven policing means aggressive police presence, surveillance, and perceived harassment in those communities. Each data point translates to real human experience, and many times those experiences remain fraught with all-too-human bias, fear, distrust, and racial tension. For those communities, especially poor communities of color, these data-collection efforts cast a dark shadow on the future.”
“Data-driven policing means aggressive police presence, surveillance, and perceived harassment in those communities. Each data point translates to real human experience, and many times those experiences remain fraught with all-too-human bias, fear, distrust, and racial tension. For those communities, especially poor communities of color, these data-collection efforts cast a dark shadow on the future.”