Amazon worker demands company stop selling facial recognition tech to law enforcement
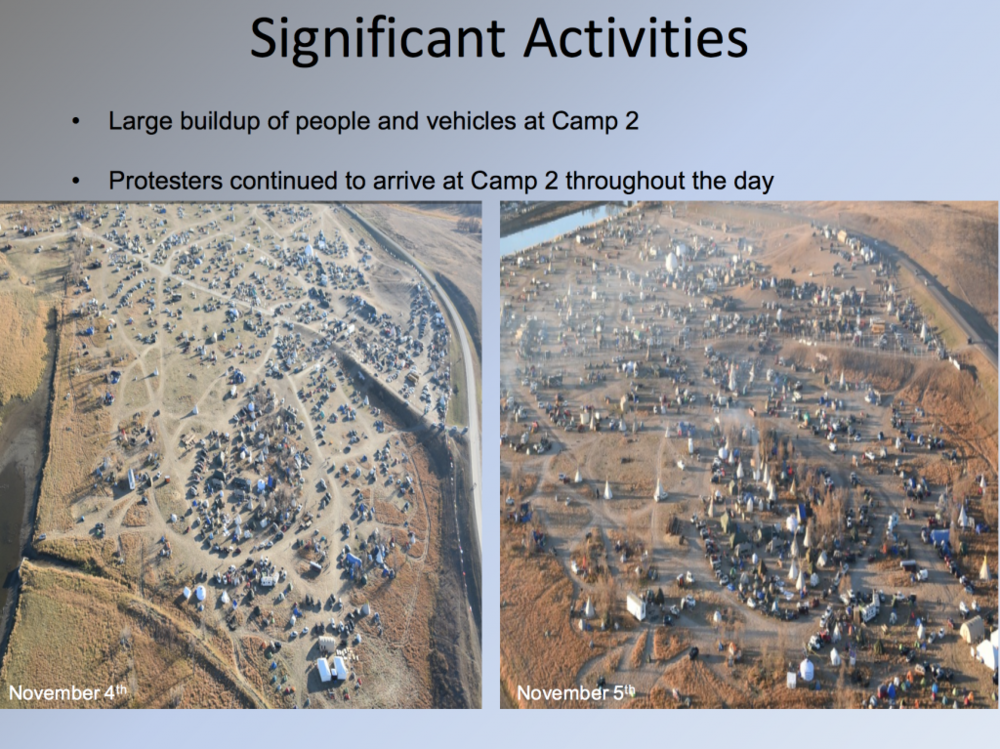
An Amazon employee is seeking to put new pressure on the company to stop selling its facial recognition technology to law enforcement. An anonymous worker, whose employment at Amazon was verified by Medium, published an op-ed on that platform on Tuesday criticizing the company’s facial recognition work and urging the company to respond to an open letter delivered by a group of employees. The employee wrote that the government has used surveillance tools in a way that disproportionately hurts “communities of color, immigrants, and people exercising their First Amendment rights.”
“Ignoring these urgent concerns while deploying powerful technologies to government and law enforcement agencies is dangerous and irresponsible,” the person wrote. “That’s why we were disappointed when Teresa Carlson, vice president of the worldwide public sector of Amazon Web Services, recently said that Amazon ‘unwaveringly supports’ law enforcement, defense, and intelligence customers, even if we don’t ‘know everything they’re actually utilizing the tool for.'” The op-ed comes one day after Amazon CEO Jeff Bezos defended technology companies working with the federal government on matters of defense during Wired’s ongoing summit in San Francisco. “If big tech companies are going to turn their back on the U.S. Department of Defense, this country is going to be in trouble,” Bezos said on Monday.

 “Data-driven policing means aggressive police presence, surveillance, and perceived harassment in those communities. Each data point translates to real human experience, and many times those experiences remain fraught with all-too-human bias, fear, distrust, and racial tension. For those communities, especially poor communities of color, these data-collection efforts cast a dark shadow on the future.”
“Data-driven policing means aggressive police presence, surveillance, and perceived harassment in those communities. Each data point translates to real human experience, and many times those experiences remain fraught with all-too-human bias, fear, distrust, and racial tension. For those communities, especially poor communities of color, these data-collection efforts cast a dark shadow on the future.” “An ambitious project to blanket New York and London with ultrafast Wi-Fi via so-called “smart kiosks,” which will replace obsolete public telephones, are the work of a Google-backed startup.
“An ambitious project to blanket New York and London with ultrafast Wi-Fi via so-called “smart kiosks,” which will replace obsolete public telephones, are the work of a Google-backed startup.